Obtaining a Long-Term Valid Login Command¶
Scenario¶
This section describes how to obtain a login command that is valid for a year.
Note
For security purposes, it is advised to obtain the login command in the development environment.
Procedure¶
Obtain the region project name and image repository address.
Log in to the management console, click your username in the upper right corner, and click My Credentials.
On the Project List tab page, search for the project corresponding to the current region.
Obtain the image repository address by referring to 1.b. The domain name at the end of the login command is the image repository address.
Obtain an AK/SK.
Note
The access key ID (AK) and secret access key (SK) are a pair of access keys used together to authenticate users who wish to make API requests. The AK/AS pair provides functions similar to a password. If you already have an AK/SK, skip this step.
Log in to the management console, click your username in the upper right corner, and click My Credentials.
On the Access Keys tab page, click Add Access Key.
Enter the login password and verification code sent to your mailbox or mobile phone.
Download the access key, which includes the AK and SK.
Note
Keep the access key secure and do not disclose it to any unauthorized personnel.
Log in to a Linux PC and run the following command to obtain the login key:
printf "$AK" | openssl dgst -binary -sha256 -hmac "$SK" | od -An -vtx1 | sed 's/[ \n]//g' | sed 'N;s/\n//'
In the command, $AK and $SK indicate the AK and SK obtained in Step 2 respectively.
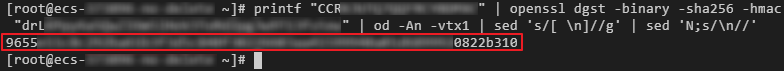
Figure 1 Sample command output¶
Put the information you obtained in the following format to generate a long-term valid login command:
docker login -u [Regional project name]@[AK] -p [Login key] [Image repository address]
In the command, the regional project name and image repository address are obtained in Step 1, the AK in Step 2, and the login key in Step 3.
Note
The login key is encrypted and cannot be decrypted. Therefore, other users cannot obtain the SK from -p.
The login command can be used on other devices.
Run the history -c command to clear the operation records.