AK/SK Authentication¶
When you use API Gateway to send requests to underlying services, the requests must be signed using the AK and SK.
Note
AK is a unique identifier that is associated with a secret access key; the access key ID and secret access key are used together to sign requests cryptographically.
SK is a key that is used in conjunction with an access key ID to cryptographically sign requests. Signing a request identifies the sender and prevents the request from being altered.
The AK/SK authentication process is as follows:
A standard request is created.
A to-be-signed string is created using the request and other related information.
A signature is calculated using the AK/SK and to-be-signed string.
The generated signature is added as a header or a query parameter in the HTTP request.
After receiving the request, API Gateway performs 1 to 3 to calculate a signature.
The new signature is compared with the signature generated in 3. If they are consistent, the request is processed; otherwise, the request is rejected.
Figure 1 shows the process of calling APIs through AK/SK authentication.
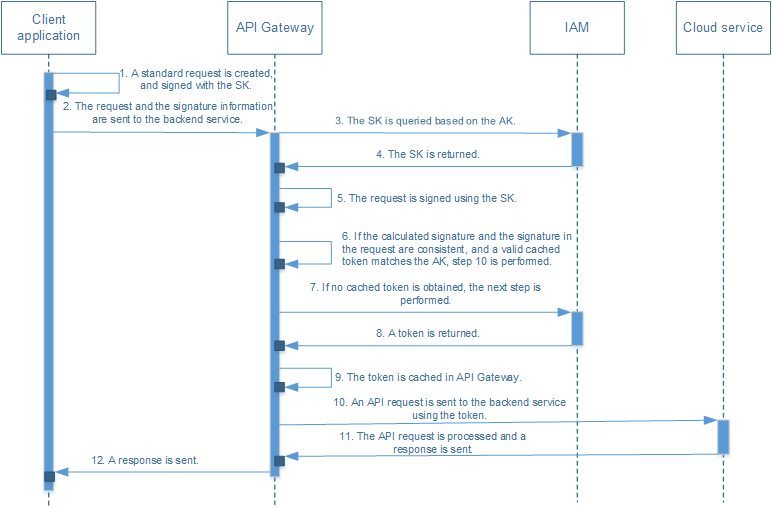
Figure 1 API calling process flow¶
Note
If a failure occurs in any step, the failure will be returned to the client application.
The cached token is valid for 15 minutes by default.