- User Guide
- API Policies
- Third-Party Authorizer
Third-Party Authorizer¶
You can configure your own service to authenticate API requests. APIG first invokes this service for authentication, and then invokes the backend service after receiving a success response.
Note
If your gateway does not support this policy, contact technical support to upgrade the gateway to the latest version.
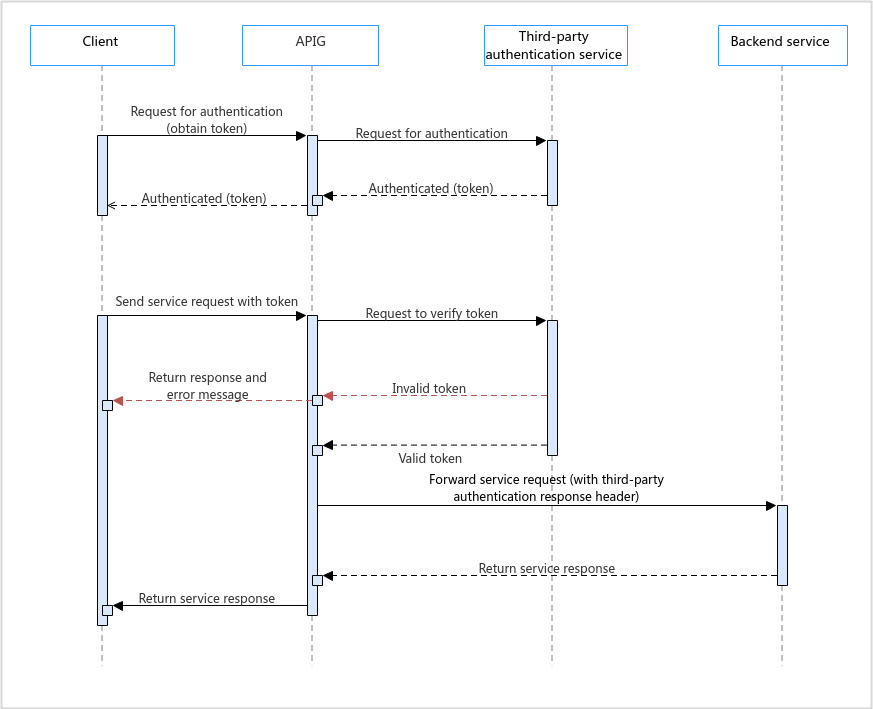
The following figure shows the principle of third-party authentication. After binding a third-party authentication policy to an API, call the API by referring to Calling APIs.
Prerequisites¶
You have understood the guidelines for policy creation and API binding.
Configuration Parameters¶
Parameter | Description |
|---|---|
Load Balance Channel | Whether to connect a third-party authentication service using a load balance channel.
|
Backend URL |
|
Timeout (ms) | Timeout of the authentication service. It cannot exceed the max. timeout of the backend service. View the timeout limit on the Parameters tab of the gateway details page. |
Host Header | Set this parameter only if a load balance channel is used. Define a host header for requests to be sent to cloud servers associated with the load balance channel. By default, the original host header in each request is used. |
Brute Force Threshold | IP addresses whose number of third-party authentication failure attempts within 5 minutes exceeds this threshold will be blocked. They will be unblocked after 5 minutes. For example, if an IP address has failed third-party authentication more than the configured threshold in the third minute, the address is blocked, and will be unblocked after 2 minutes. |
Identity Sources | Parameters to obtain from the original API requests for third-party authentication. Max. 10 headers and 10 query strings. If not specified, all headers and query strings in the original requests will be used. |
Relaxed Mode | When this option is enabled, APIG accepts client requests even when your authentication service cannot connect or returns an error code starting with "5". |
Allow Original Request Body | When this option is enabled, the original request body is included for authentication. |
Request Body Size (bytes) | Available only when Allow Original Request Body is enabled. The value cannot exceed the max. request body size of the gateway. View the request body size limit on the Parameters tab of the gateway details page. |
Allow Original Request Path | When this option is enabled, the original request path is added to the end of the authentication request path. |
Return Response | When this option is enabled, the authentication response is returned on failure. |
Allowed Response Headers | Headers to obtain from the authentication response and send to the backend service, when the authentication is successful. Max. 10 headers. |
Simple Authentication | When this option is enabled, status codes starting with "2" indicate successful authentication. |
Authentication Result | Available only when Simple Authentication is disabled. Responses whose headers contain these parameters with the same values indicate successful authentication. |
Blacklist/Whitelist | When this option is enabled, whether API requests require third-party authentication depends on the configured blacklist or whitelist rules. |
Type |
|
Parameters | Define parameters for rule matching.
|
Rules | Define conditions for rule matching. Click Add Rule and edit the rule name and conditions. In the Condition Expressions dialog box, select a parameter and operator, and enter a value.
|
Example Script¶
{
"auth_request": {
"method": "GET",
"protocol": "HTTPS",
"url_domain": "192.168.10.10",
"timeout": 5000,
"path": "/",
"vpc_channel_enabled": false,
"vpc_channel_info": null
},
"custom_forbid_limit": 100,
"carry_body": {
"enabled": true,
"max_body_size": 1000
},
"auth_downgrade_enabled": true,
"carry_path_enabled": true,
"return_resp_body_enabled": false,
"carry_resp_headers": [],
"simple_auth_mode_enabled": true,
"match_auth": null,
"rule_enabled": false,
"rule_type": "allow"
}