Using LTS to Log WAF Activities¶
After you authorize WAF to access Log Tank Service (LTS), you can use the WAF logs recorded by LTS for quick and efficient real-time analysis, device O&M management, and analysis of service trends.
LTS analyzes and processes a large number of logs. It enables you to process logs in real-time, efficiently, and securely. Logs can be stored in LTS for 30 days by default but you can configure LTS for up to 365 days if needed. Logs earlier than storage duration are automatically deleted. However, you can configure LTS to dump those logs to an Object Storage Service (OBS) bucket or enable Data Ingestion Service (DIS) for long-term storage.
Prerequisites¶
You have applied for your WAF.
Impact on the System¶
Enabling LTS for WAF does not affect WAF performance.
Enabling LTS for WAF Protection Event Logging¶
Log in to the management console.
Click
 in the upper left corner and select a region or project.
in the upper left corner and select a region or project.Click
 in the upper left corner and choose Web Application Firewall (Dedicated) under Security.
in the upper left corner and choose Web Application Firewall (Dedicated) under Security.In the navigation pane on the left, click Events.
Click the Configure Logs or Log Settings tab, enable LTS (
 ), and select a log group and log stream. Table 1 describes the parameters.
), and select a log group and log stream. Table 1 describes the parameters.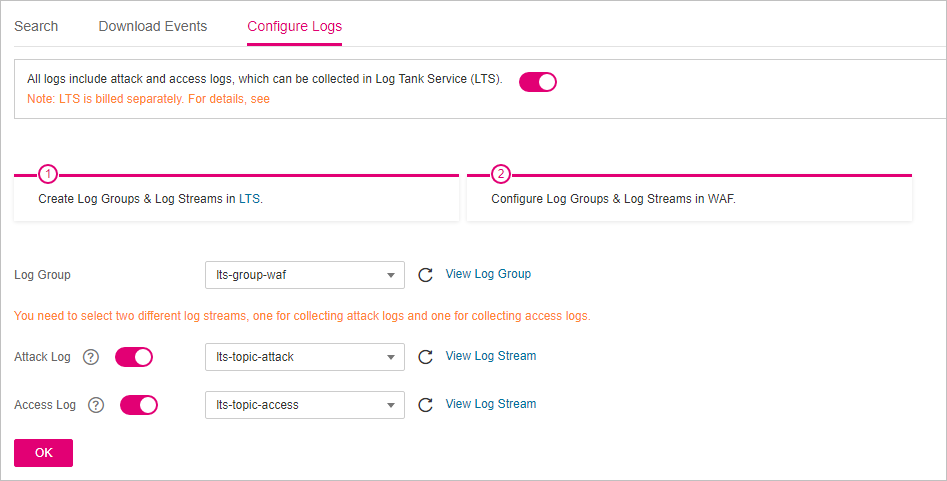
Figure 1 Log settings¶
Table 1 Log configuration¶ Parameter
Description
Example Value
Log Group
Select a log group or click View Log Group to go to the LTS console and create a log group.
lts-group-waf
Attack Log
Select a log stream or click View Log Stream to go to the LTS console and create a log stream.
An attack log includes information about event type, protective action, and attack source IP address of each attack.
lts-topic-waf-attack
Access Log
Select a log stream or click View Log Stream to go to the LTS console and create a log stream.
An access log includes key information about access time, client IP address, and resource URL of each HTTP access requests.
lts-topic-waf-access
Click OK.
You can view WAF protection event logs on the LTS console.
Checking and Downloading WAF Protection Event Logs on LTS¶
After enabling LTS, you can go to the LTS console and check, analyze, and download WAF logs.
Log in to the management console.
Click
 in the upper left corner of the management console and select a region or project.
in the upper left corner of the management console and select a region or project.Click
 in the upper left corner of the page and choose Management & Deployment > Log Tank Service.
in the upper left corner of the page and choose Management & Deployment > Log Tank Service.In the log group list, click
 to expand the WAF log group (for example, lts-group-waf).
to expand the WAF log group (for example, lts-group-waf).In the log stream list, click the log stream name to go to the log stream log page. Then, you can check and analyze logs.
WAF access_log Field Description¶
Field | Type | Field Description | Description |
|---|---|---|---|
access_log.requestid | String | Random ID | The value is the same as the last eight characters of the req_id field in the attack log. |
access_log.time | String | Access time | GMT time a log is generated. |
access_log.connection_requests | String | Sequence number of the request over the connection |
|
access_log.eng_ip | String | IP address of the WAF engine |
|
access_log.pid | String | The engine that processes the request | Engine (worker PID). |
access_log.hostid | String | Domain name identifier of the access request. | Protected domain name ID (upstream_id). |
access_log.tenantid | String | Account ID | Each account corresponds to a tenant ID. |
access_log.projectid | String | ID of the project the protected domain name belongs to | Project ID of a user in a specific region. |
access_log.remote_ip | String | Remote IP address of the request at layer 4 | IP address from which a client request originates. Important NOTICE: If a layer-7 proxy is deployed in front of WAF, this field indicates the IP address of the proxy node closest to WAF. The real IP address of the visitor is specified by the x-forwarded-for and x_real_ip fields. |
access_log.remote_port | String | Remote port of the request at layer 4 | Port used by the IP address from which a client request originates |
access_log.sip | string | IP address of the client that sends the request | For example, XFF. |
access_log.scheme | String | Request protocol | Protocols that can be used in the request:
|
access_log.response_code | String | Response code | Response status code returned by the origin server to WAF. |
access_log.method | String | Request method. | Request type in a request line. Generally, the value is GET or POST. |
access_log.http_host | String | Domain name of the requested server. | Address, domain name, or IP address entered in the address bar of a browser. |
access_log.url | String | Request URL. | Path in a URL (excluding the domain name). |
access_log.request_length | String | Request length. | The request length includes the access request address, HTTP request header, and number of bytes in the request body. |
access_log.bytes_send | String | Total number of bytes sent to the client. | Number of bytes sent by WAF to the client. |
access_log.body_bytes_sent | String | Total number of bytes of the response body sent to the client | Number of bytes of the response body sent by WAF to the client |
access_log.upstream_addr | String | Address of the backend server. | IP address of the origin server for which a request is destined. For example, if WAF forwards requests to an ECS, the IP address of the ECS is returned to this parameter. |
access_log.request_time | String | Request processing time | Processing time starts when the first byte of the client is read (unit: s). |
access_log.upstream_response_time | String | Backend server response time | Time the backend server responds to the WAF request (unit: s). |
access_log.upstream_status | String | Backend server response code | Response status code returned by the backend server to WAF. |
access_log.upstream_connect_time | String | Time for the origin server to establish a connection to its backend services. Unit: second. | When SSL is used, the time for the handshake process is also recorded. Time used for establishing a connection for a request. Use commas (,) to separate the time used for each request. |
access_log.upstream_header_time | String | Time used by the backend server to receive the first byte of the response header. Unit: second | Response time for multiple requests. Use commas (,) to separate the time used for each response. |
access_log.bind_ip | String | WAF engine back-to-source IP address. | The IP address of the NIC used by the engine for forwarding requests to the origin server. This value is not the EIP bound to the engine even if the engine forwards requests over the EIP. |
access_log.group_id | String | LTS log group ID | ID of the log group for interconnecting WAF with LTS. |
access_log.access_stream_id | String | Log stream ID. | ID of access_stream of the user in the log group identified by the group_id field. |
access_log.engine_id | String | WAF engine ID | Unique ID of the WAF engine. |
access_log.time_iso8601 | String | ISO 8601 time format of logs. |
|
access_log.sni | String | Domain name requested through SNI. |
|
access_log.tls_version | String | Protocol versioning an SSL connection. | TLS version used in the request. |
access_log.ssl_curves | String | Curve group list supported by the client. |
|
access_log.ssl_session_reused | String | SSL session reuse | Whether the SSL session can be reused r: Yes .: No |
access_log.process_time | String | Engine attack detection duration (unit: ms) |
|
access_log.args | String | The parameter data in the URL |
|
access_log.x_forwarded_for | String | IP address chain for a proxy when the proxy is deployed in front of WAF. | The sting includes one or more IP addresses. The leftmost IP address is the originating IP address of the client. Each time the proxy server receives a request, it adds the source IP address of the request to the right of the originating IP address. |
access_log.cdn_src_ip | String | Client IP address identified by CDN when CDN is deployed in front of WAF | This field specifies the real IP address of the client if CDN is deployed in front of WAF. Important NOTICE: Some CDN vendors may use other fields. WAF records only the most common fields. |
access_log.x_real_ip | String | Real IP address of the client when a proxy is deployed in front of WAF. | Real IP address of the client, which is identified by the proxy. |
access_log.intel_crawler | String | Used for intelligence anti-crawler analysis. |
|
access_log.ssl_ciphers_md5 | String | MD5 value of the SSL cipher (ssl_ciphers). |
|
access_log.ssl_cipher | String | SSL cipher used. |
|
access_log.web_tag | String | Website name. |
|
access_log.user_agent | String | User agent in the request header. |
|
access_log.upstream_response_length | String | Backend server response size. |
|
access_log.region_id | String | Region where the request is received. |
|
access_log.enterprise_project_id | String | ID of the enterprise project that the requested domain name belongs to. |
|
access_log.referer | String | Referer content in the request header. | The value can contain a maximum of 128 characters. Characters over 128 characters will be truncated. |
access_log.rule | String | Protection rule that the request matched. | If multiple rules are matched, only one rule is displayed. |
access_log.category | String | Log category matched by the request. |
|
access_log.waf_time | String | Time an access request is received. |
|
access_log.geo | String | Mark of geographical location. |
|
WAF attack_log Field Description¶
Field | Type | Field Description | Description |
|---|---|---|---|
attack_log.category | String | Log category | The value is attack. |
attack_log.time | String | Log time |
|
attack_log.time_iso8601 | String | ISO 8601 time format of logs. |
|
attack_log.policy_id | String | Policy ID |
|
attack_log.level | String | Protection level | Protection level of a built-in rule in basic web protection
|
attack_log.attack | String | Type of attack | Attack type. This parameter is listed in attack logs only.
|
attack_log.action | String | Protective action | WAF defense action.
|
attack_log.sub_type | String | Crawler types | When attack is set to robot, this parameter cannot be left blank.
|
attack_log.rule | String | ID of the triggered rule or the description of the custom policy type. |
|
attack_log.rule_name | String | Description of a custom rule type. | This field is empty when a basic protection rule is matched. |
attack_log.location | String | Location triggering the malicious load |
|
attack_log.req_body | sting | Request body. |
|
attack_log.resp_headers | String | Response header |
|
attack_log.hit_data | String | String triggering the malicious load |
|
attack_log.resp_body | String | Response body |
|
attack_log.backend.protocol | String | Backend protocol. |
|
attack_log.backend.alive | String | Backend server status. |
|
attack_log.backend.port | String | Backend server port. |
|
attack_log.backend.host | String | Backend server host value. |
|
attack_log.backend.type | String | Backend server type. | IP address or domain name. |
attack_log.backend.weight | number | Backend server weight. |
|
attack_log.status | String | Response status code |
|
attack_log.upstream_status | String | Origin server response code. |
|
attack_log.reqid | String | Random ID | The value consists of the engine IP address suffix, request timestamp, and request ID allocated by Nginx. |
attack_log.requestid | String | Unique ID of the request. | Request ID allocated by Nginx. |
attack_log.id | String | Attack ID | ID of the attack |
attack_log.method | String | Request method |
|
attack_log.sip | String | Client request IP address |
|
attack_log.sport | String | Client request port |
|
attack_log.host | String | Requested domain name |
|
attack_log.http_host | String | Domain name of the requested server. |
|
attack_log.hport | String | Port of the requested server. |
|
attack_log.uri | String | Request URL. | The domain is excluded. |
attack_log.header | A JSON string. A JSON table is obtained after the string is decoded. | Request header |
|
attack_log.mutipart | A JSON string. A JSON table is obtained after the string is decoded. | Request multipart header | This parameter is used to upload files. |
attack_log.cookie | A JSON string. A JSON table is obtained after the string is decoded. | Cookie of the request |
|
attack_log.params | A JSON string. A JSON table is obtained after the string is decoded. | Params value following the request URI. |
|
attack_log.body_bytes_sent | String | Total number of bytes of the response body sent to the client. | Total number of bytes of the response body sent by WAF to the client. |
attack_log.upstream_response_time | String | Time elapsed since the backend server received the response content from the upstream service. Unit: second. | Response time for multiple requests. Use commas (,) to separate the time used for each response. |
attack_log.engine_id | String | Unique ID of the engine |
|
attack_log.region_id | String | ID of the region where the engine is located. |
|
attack_log.engine_ip | String | Engine IP address. |
|
attack_log.process_time | String | Detection duration |
|
attack_log.remote_ip | String | Layer-4 IP address of the client that sends the request. |
|
attack_log.x_forwarded_for | String | Content of X-Forwarded-For in the request header. |
|
attack_log.cdn_src_ip | String | Content of Cdn-Src-Ip in the request header. |
|
attack_log.x_real_ip | String | Content of X-Real-IP in the request header. |
|
attack_log.group_id | String | Log group ID | LTS log group ID |
attack_log.attack_stream_id | String | Log stream ID | ID of access_stream of the user in the log group identified by the group_id field. |
attack_log.hostid | String | Protected domain name ID (upstream_id). |
|
attack_log.tenantid | String | Account ID |
|
attack_log.projectid | String | ID of the project the protected domain name belongs to |
|
attack_log.enterprise_project_id | String | ID of the enterprise project that the requested domain name belongs to. |
|
attack_log.web_tag | String | Website name. |
|
attack_log.req_body | String | Request body. (If the request body larger than 1 KB, it will be truncated.) |
|