Configuring a CC Attack Protection Rule¶
You can customize a CC attack protection rule to restrict access to a specific URL on your website based on an IP address, cookie, or Referer, mitigating CC attacks. To make your custom CC attack protection rules take effect, ensure that you have enabled CC attack protection.
Note
If you have enabled enterprise projects, ensure that you have all operation permissions for the project where your WAF instance locates. Then, you can select the project from the Enterprise Project drop-down list and configure protection policies for the domain names in the project.
Prerequisites¶
A website has been added to WAF.
Constraints¶
It takes several minutes for a new rule to take effect. After the rule takes effect, protection events triggered by the rule will be displayed on the Events page.
A reference table can be added to a CC attack protection rule. The reference table takes effect for all protected domain names.
A CC attack protection rule offers protective actions such as Verification code and Block for your choice. For example, you can configure a CC attack protection rule to block requests from a visit for 600 seconds by identifying their cookie (name field) if the visitor accessed a URL (for example, /admin*) of your website over 10 times within 60 seconds.
Procedure¶
Log in to the management console.
Click
 in the upper left corner of the management console and select a region or project.
in the upper left corner of the management console and select a region or project.Click
 in the upper left corner and choose Web Application Firewall (Dedicated) under Security.
in the upper left corner and choose Web Application Firewall (Dedicated) under Security.In the navigation pane on the left, choose Website Settings.
In the Policy column of the row containing the target website, click the number to go to the policy configuration page.
In the CC Attack Protection configuration area, change Status if needed and click Customize Rule to go to the CC Attack Protection page.
Figure 1 CC Attack Protection configuration area¶
In the upper left corner of the CC Attack Protection page, click Add Rule.
In the displayed dialog box, configure a CC attack protection rule by referring to Table 1.
If a visitor whose cookie is name accesses a page on your website where the address includes /admin at the end (for example, https://www.example.com/adminlogic) more than 10 times within 60 seconds, WAF blocks the requests from visitors of the same cookie name for 600s and returns the page configured for Page Content. Figure 2 shows the configurations.
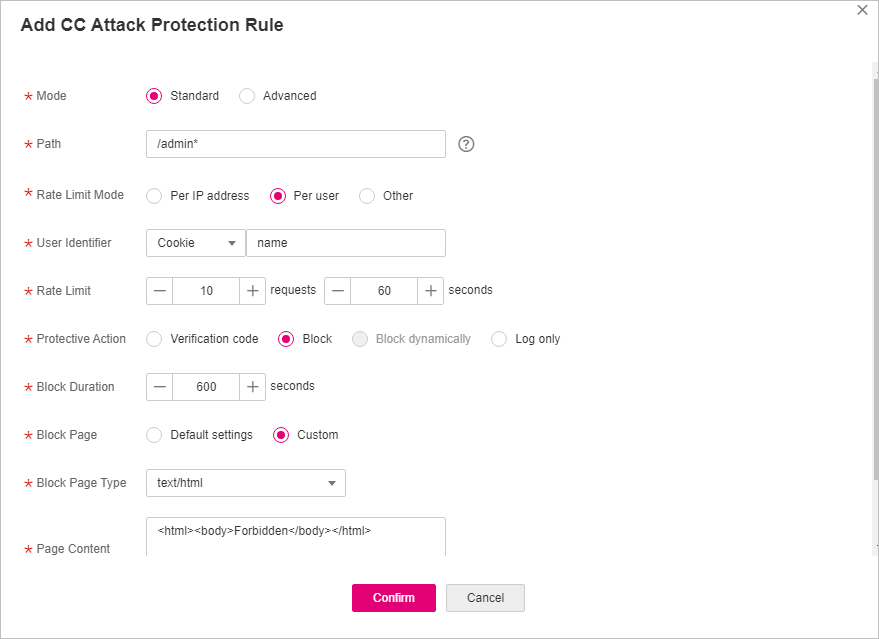
Figure 2 Adding a CC attack protection rule¶
Table 1 Rule parameters¶ Parameter
Description
Example Value
Mode
Standard: Only the protection path of a domain name can be restricted.
Advanced: The path, IP address, cookie, header, and params fields can all be restricted.
Standard
Path
Set this parameter only when Standard is selected for Mode.
Part of the URL without the domain name.
Prefix match: A path ending with * indicates that the path is used as a prefix. The * can be used as a wildcard value. For example, to protect /admin/test.php or /adminabc, you can set Path to /admin*.
Exact match: The path to be entered must be the same as the path to be protected. For example, to protect /admin, then Path must be set to /admin.
Note
The path supports prefix and exact matches only but does not support regular expressions.
The path cannot contain two or more consecutive slashes. For example, ///admin. If you enter ///admin, WAF will convert /// to /.
The path is case-sensitive.
If Path is set to /, all paths of the website are protected.
/admin*
Condition List
Set this parameter only when Advanced is selected for Mode.
Click Add to add conditions. At least one condition is required, but up to 30 conditions are allowed. If you add more than one condition, the rule will only take effect if all of the conditions are met.
Field: The options are Path, IP, Cookie, Header, and Params.
Subfield: Configure this field only when Cookie, Header, or Params is selected for Field.
Important
NOTICE: The length of a subfield cannot exceed 2048 bytes. Only digits, letters, underscores (_), and hyphens (-) are allowed.
Logic: Select a logical relationship from the drop-down list.
Note
If you set Logic to Include any value, Exclude any value, Equal to any value, Not equal to any value, Prefix is any value, Prefix is not any of them, Suffix is any value, or Suffix is not any of them, select an existing reference table. For details, see Adding a Reference Table.
Content: Enter or select the content that matches the condition.
Path Include /admin
Rate Limit Mode
Per IP address: A website visitor is identified by the IP address.
Per user: A website visitor is identified by the key value of Cookie or Header.
Other: A website visitor is identified by the Referer field (user-defined request source).
Note
If you set Rate Limit Mode to Other, set Content of Referer to a complete URL containing the domain name. The Content field supports prefix match and exact match only, but cannot contain two or more consecutive slashes, for example, ///admin. If you enter ///admin, WAF will convert it to /admin.
For example, if Path is /admin, and you do not want visitors to access the page from www.test.com, set Content of Referer to http://www.test.com.
Per user
User Identifier
This parameter is mandatory when you select Per user for Rate Limit Mode.
Cookie: A cookie field name. You need to configure an attribute variable name in the cookie that can uniquely identify a web visitor based on your website requirements. This field does not support regular expressions. Only complete matches are supported.
For example, if a website uses the name field in the cookie to uniquely identify a website visitor, select name.
Header: Set the user-defined HTTP header you want to protect. You need to configure the HTTP header that can identify web visitors based on your website requirements.
name
Rate Limit
The number of requests allowed from a website visitor in the rate limit period. If the number of requests exceeds the rate limit, WAF takes the action you configure for Protective Action.
All WAF instances: Requests to on one or more WAF instances will be counted together according to the rate limit mode you select. By default, requests to each WAF instance are counted. If you enable this, WAF will count requests to all your WAF instances for triggering this rule. To enable user-based rate limiting, Per user or Other (Referer must be configured) instead of Per IP address must be selected for Rate Limit Mode. This is because IP address-based rate limiting cannot limit the access rate of a specific user. However, in user-based rate limiting, requests may be forwarded to one or more WAF instances. Therefore, All WAF instances must be enabled for triggering the rule precisely.
10 requests allowed in 60 seconds
Protective Action
The action that WAF will take if the number of requests exceeds Rate Limit you configured. The options are as follows:
Verification code: WAF allows requests that trigger the rule as long as your website visitors complete the required verification.
Block: WAF blocks requests that trigger the rule.
Block dynamically: WAF blocks requests that trigger the rule based on Allowable Frequency, which you configure after the first rate limit period is over.
The protective action is supported only when Advanced is selected for Mode.
Log only: WAF only logs requests that trigger the rule. You can download event data and view the protection logs of a specific domain name.
Block
Allowable Frequency
This parameter can be set if you select Block dynamically for Protective Action.
WAF blocks requests that trigger the rule based on Rate Limit first. Then, in the following rate limit period, WAF blocks requests that trigger the rule based on Allowable Frequency you configure.
Allowable Frequency cannot be larger than Rate Limit.
Note
If you set Allowable Frequency to 0, WAF blocks all requests that trigger the rule in the next rate limit period.
8 requests allowed in 60 seconds
Block Duration
Period of time for which to block the item when you set Protective Action to Block.
600 seconds
Block Page
The page displayed if the maximum number of requests has been reached. This parameter is configured only when Protective Action is set to Block.
If you select Default settings, the default block page is displayed.
If you select Custom, a custom error message is displayed.
Custom
Block Page Type
If you select Custom for Block Page, select a type of block page. The options are:
application/jsontext/html
text/htmltext/xml
text/xml
text/html
Page Content
If you select Custom for Block Page, configure the content to be returned.
Page content styles corresponding to different page types are as follows:
text/html: <html><body>Forbidden</body></html>
application/json: {"msg": "Forbidden"}
text/xml: <?xml version="1.0" encoding="utf-8"?><error> <msg>Forbidden</msg></error>
Rule Description
A description of the rule. This parameter is optional.
None
Click Confirm. You can then view the added CC attack protection rule in the CC rule list.
To disable a rule, click Disable in the Operation column of the rule. The default Rule Status is Enabled.
To modify a rule, click Modify in the row containing the rule.
To delete a rule, click Delete in the row containing the rule.
Protection Effect¶
If you have configured a CC attack protection rule for your domain name, with Protective Action set to Block, as shown in Figure 2, to verify WAF is protecting your website (www.example.com) against the configured CC attack protection rule:
Clear the browser cache and enter the domain name in the address box of a browser to check whether the website is accessible.
If the website is inaccessible, connect the website domain name to WAF by following the instructions in Step 1: Add a Website to WAF.
If the website is accessible, go to Step 2.
Clear the browser cache, enter http://www.example.com/admin in the address bar, and refresh the page 10 times within 60 seconds. In normal cases, the custom block page will be displayed the eleventh time you refresh the page, and the requested page will be accessible when you refresh the page 600 seconds later.
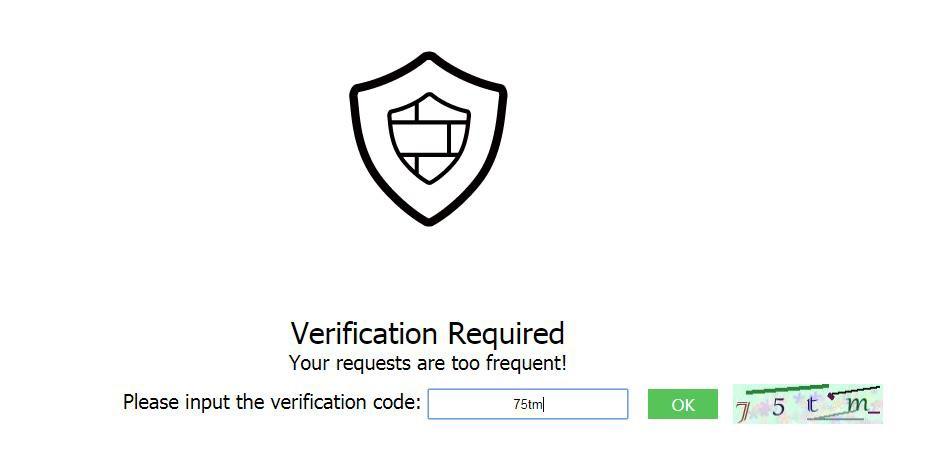
If you select Verification code for protective action, a verification code is required for visitors to continue the access if they exceed the configured rate limit.
Return to the WAF console. In the navigation pane, choose Events. On the displayed page, view or download events data.
Configuration Example - Verification Code¶
If domain name www.example.com has been connected to WAF, perform the following steps to verify that WAF CAPTCHA verification is enabled.
Add a CC attack protection rule with Protection Action set to Verification code.
Enable CC attack protection.
Figure 3 CC Attack Protection configuration area¶
Clear the browser cache and access http://www.example.com/admin/.
If you access the page for 10 times within 60 seconds, a verification code is required when you attempt to access the page for the eleventh time. You need to enter the verification code to continue the access.
Go to the WAF console. In the navigation pane on the left, choose Events. View the event on the Events page.