Handling False Alarms¶
If you confirm that an attack event on the Events page is a false alarm, you can handle the event as false alarm by ignoring the URL and rule ID in basic web protection, or by deleting or disabling the corresponding protection rule you configured. After an attack event is handled as a false alarm, the event will not be displayed on the Events page anymore. You will no longer receive any alarm notifications about the event.
WAF detects attacks by using built-in basic web protection rules, built-in features in anti-crawler protection, and custom rules you configured (such as CC attack protection, precise access protection, blacklist, whitelist, and geolocation access control rules). WAF will respond to detected attacks based on the protective actions (such as Block and Log only) defined in the rules and display attack events on the Events page.
Prerequisites¶
There is at least one false alarm event in the event list.
Constraints¶
Only attack events blocked or recorded by preconfigured basic web protection rules and features in anti-crawler protection can be handled as false alarms.
For events generated based on custom rules (such as a CC attack protection rule, precise protection rule, blacklist rule, whitelist rule, or geolocation access control rule), they cannot be handled as false alarms. To ignore such an event, delete or disable the custom rule hit by the event.
An attack event can only be handled as a false alarm once.
Application Scenarios¶
Sometimes normal service requests may be blocked by WAF. For example, suppose you deploy a web application on an ECS and then add the public domain name associated with that application to WAF. If you enable basic web protection for that application, WAF may block the access requests that match the basic web protection rules. As a result, the website cannot be accessed through its domain name. However, the website can still be accessed through the IP address. In this case, you can handle the false alarms to allow normal access requests to the application.
Impact on the System¶
The attack event will not be displayed on the Events page. You will no longer receive any alarm notifications about the event.
Procedure¶
Log in to the management console.
Click
 in the upper left corner of the management console and select a region or project.
in the upper left corner of the management console and select a region or project.Click
 in the upper left corner and choose Web Application Firewall (Dedicated) under Security.
in the upper left corner and choose Web Application Firewall (Dedicated) under Security.In the navigation pane on the left, choose Events.
Select the Search tab. Select a website from the All protected websites drop-down list. Then, select Yesterday, Today, Past 3 days, Past 7 days, Past 30 days, or a custom time range. Table 1 and Table 2 describe parameters.
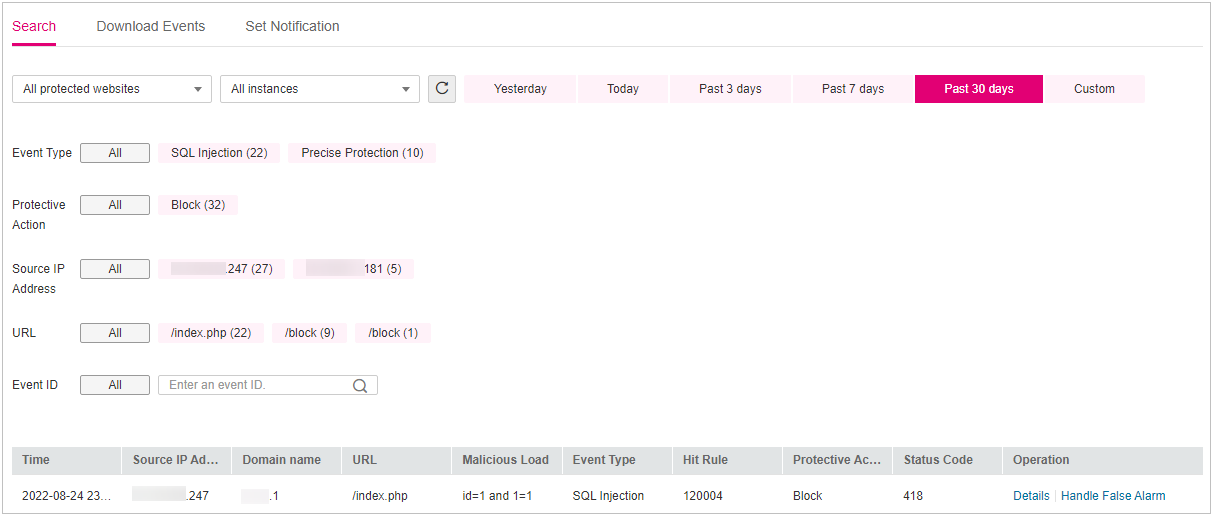
Figure 1 Viewing protection events¶
Table 1 Event parameters¶ Parameter
Description
Event Type
Type of attack.
By default, All is selected. You can view logs of all attack types or select an attack type to view corresponding attack logs.
Protective Action
The options are Block, Log only, and Verification code.
Source IP Address
Public IP address of the web visitor/attacker
By default, All is selected. You can view logs of all attack source IP addresses, select an attack source IP address, or enter an attack source IP address to view corresponding attack logs.
URL
Attacked URL
Event ID
ID of the event
Table 2 Parameters in the event list¶ Parameter
Description
Example Value
Time
When the attack occurred
2021/02/04 13:20:04
Source IP Address
Public IP address of the web visitor/attacker
None
Geolocation
Location where the IP address of the attack originates from
-Domain Name
Attacked domain name
www.example.com
URL
Attacked URL
/admin
Malicious Load
The location or part of the attack that causes damage or the number of times that the URL was accessed.
Note
In a CC attack, the malicious load indicates the number of times that the URL was accessed.
For blacklist protection events, the malicious load is left blank.
id=1 and 1='1
Event Type
Type of attack
SQL injection
Protective Action
Protective actions configured in the rule. The options are Block, Log only, and Verification code.
Note
If an access request matches a web tamper protection rule, information leakage prevention rule, or data masking rule, the protective action is marked as Mismatch.
Block
Status Code
HTTP status code returned on the block page.
418
Note
To view event details, click Details in the Operation column of the event list.
After you confirm that an event is a false alarm, click Handle False Alarm in the Operation column of the row and add a false alarm masking rule. Table 3 describes parameters.
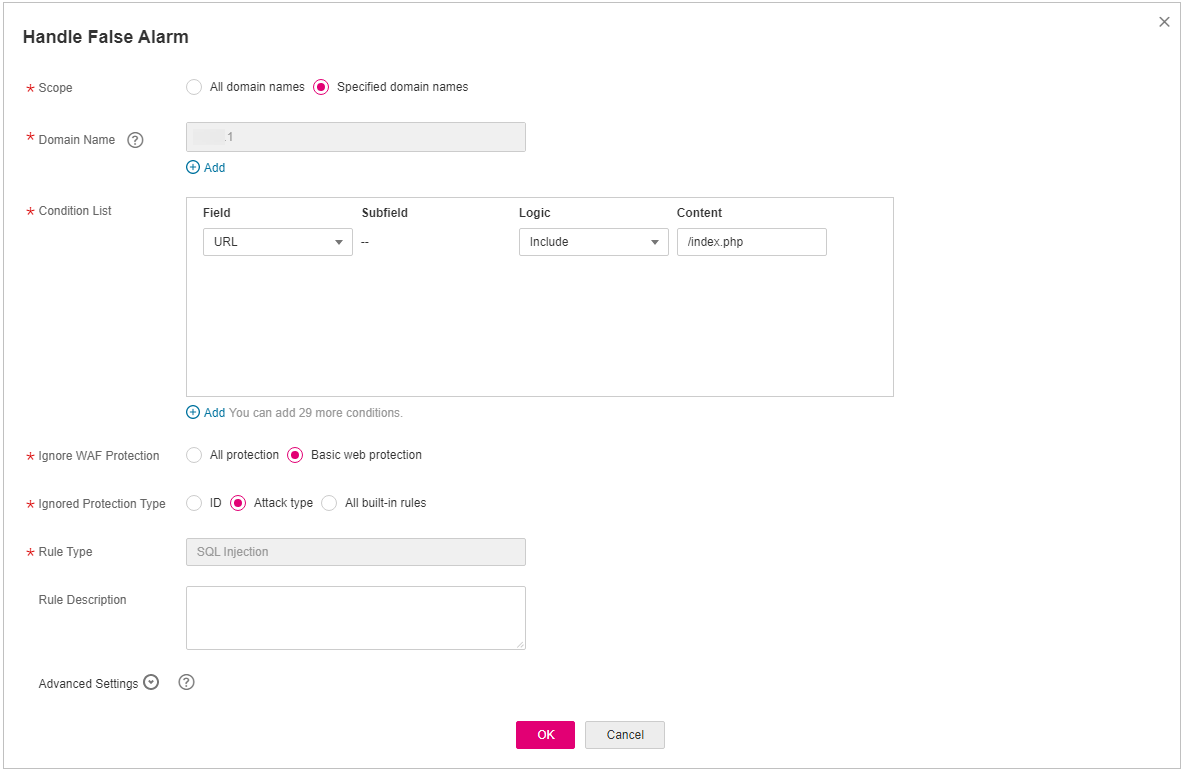
Figure 2 Handling a false alarm¶
Table 3 Parameters¶ Parameter
Description
Example Value
Scope
All domain names: By default, this rule will be used to all domain names that are protected by the current policy.
Specified domain names: This rule will be used to the specified domain names that match the wildcard domain name being protected by the current policy.
Specified domain names
Domain Name
This parameter is mandatory when you select Specified domain names for Scope.
Enter a single domain name that matches the wildcard domain name being protected by the current policy.
www.example.com
Condition List
Click Add to add conditions. At least one condition needs to be added. You can add up to 30 conditions to a protection rule. If more than one condition is added, all of the conditions must be met for the rule to be applied. A condition includes the following parameters:
Parameters for configuring a condition are described as follows:
Field
Subfield: Configure this field only when Params, Cookie, or Header is selected for Field.
Important
NOTICE: The length of a subfield cannot exceed 2,048 bytes. Only digits, letters, underscores (_), and hyphens (-) are allowed.
Logic: Select a logical relationship from the drop-down list.
Content: Enter or select the content that matches the condition.
Path, Include, /product
Ignore WAF Protection
All protection: All WAF rules do not take effect, and WAF allows all request traffic to the domain names in the rule.
Basic Web Protection: You can ignore basic web protection by rule ID, attack type, or all built-in rules. For example, if XSS check is not required for a URL, you can whitelist XSS rule.
Basic Web Protection
Ignored Protection Type
If you select Basic web protection for Ignored Protection Type, specify the following parameters:
ID: Configure the rule by event ID.
Attack type: Configure the rule by attack type, such as XSS and SQL injection. One type contains one or more rule IDs.
All built-in rules: all checks enabled in Basic Web Protection.
Attack type
ID
This parameter is mandatory when you select ID for Ignored Protection Type.
ID of an attack event on the Events page. If the event type is Custom, it has no event ID. Click Handle False Alarm in the row containing the attack event to obtain the ID. You are advised to configure global protection whitelist (formerly false alarm masking) rules on the Events page by referring to Handling False Alarms.
041046
Attack type
This parameter is mandatory when you select Attack type for Ignored Protection Type.
Select an attack type from the drop-down list box.
WAF can defend against XSS attacks, web shells, SQL injection attacks, malicious crawlers, remote file inclusions, local file inclusions, command injection attacks, and other attacks.
SQL injection
Rule Description
A brief description of the rule. This parameter is optional.
SQL injection attacks are not intercepted.
Advanced Settings
To ignore attacks of a specific field, specify the field in the Advanced Settings area. After you add the rule, WAF will stop blocking attack events of the specified field.
Select a target field from the first drop-down list box on the left. The following fields are supported: Params, Cookie, Header, Body, and Multipart.
If you select Params, Cookie, or Header, you can select All or Specified field to configure a subfield.
If you select Body or Multipart, you can select All.
If you select Cookie, the Domain Name and Path can be empty.
Note
If All is selected, WAF will not block all attack events of the selected field.
Params
All
Click OK.
Verification¶
A false alarm will be deleted within about a minute after the handling configuration is done. It will no longer be displayed in the attack event details list. You can refresh the browser cache and request the page for which the false alarm masking rule is configured to check whether the configuration takes effect.
Other Operations¶
If an event is handled as a false alarm, the rule hit will be added to the global protection whitelist (formerly false alarm masking) rule list. You can go to the Policies page and then switch to the Global Protection Whitelist (Formerly False Alarm Masking) page to manage the rule, including querying, disabling, deleting, and modifying the rule. For more details, see Configuring a Global Protection Whitelist (Formerly False Alarm Masking) Rule.