Creating a User and Granting NAT Gateway Permissions¶
This section describes how to use IAM to implement fine-grained permissions control for your NAT Gateway resources. With IAM, you can:
Create IAM users for employees based on your enterprise's organizational structure. Each IAM user will have their own security credentials for accessing NAT Gateway resources.
Grant only the permissions required for users to perform a specific task.
Entrust an account or a cloud service to perform efficient O&M on your NAT Gateway resources.
If your account does not require individual IAM users, skip this section.
This section describes the procedure for granting permissions (see Figure 1).
Prerequisites¶
Learn about the permissions supported by NAT Gateway and choose policies or roles according to your requirements. For details, see Permissions Management. For the permissions of other services, see Permissions.
Process Flow¶
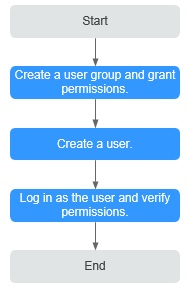
Figure 1 Process for granting NAT Gateway permissions¶
Create a user group and assign permissions.
Create a user group on the IAM console and attach the NATReadOnlyAccess policy to the group.
Create an IAM user and add it to a user group.
Create a user on the IAM console and add the user to the group created in 1.
Log in and verify permissions.
Log in to the management console as the created user. Switch to the authorized region and verify the permissions.
Choose Service List > NAT Gateway. Then click Create NAT Gateway. If a message appears indicating that you have insufficient permissions to perform the operation, the NATReadOnlyAccess policy has already taken effect.
Choose any other service in Service List. If a message appears indicating that you have insufficient permissions to access the service, the NATReadOnlyAccess policy has already taken effect.