Creating a Custom Cluster¶
The first step of using MRS is to create a cluster. This section describes how to create a cluster on the Custom Config tab of the MRS management console.
You can create an IAM user or user group on the IAM management console and grant it specific operation permissions, to perform refined resource management after registering an account. For details, see Creating an MRS User.
Log in to the MRS console.
Click Create Cluster. The page for creating a cluster is displayed.
Note
When creating a cluster, pay attention to quota notification. If a resource quota is insufficient, increase the resource quota as prompted and create a cluster.
Click the Custom Config tab.
Configure cluster information by referring to Software Configurations and click Next.
Configure cluster information by referring to Hardware Configurations and click Next.
Set advanced options by referring to Advanced Options and click Next.
If Kerberos authentication is enabled for a cluster, check whether Kerberos authentication is required. If yes, click Continue. If no, click Back to disable Kerberos authentication and then create a cluster.
Note
For any doubt about the pricing, click Pricing details in the lower left corner.
On the Confirm Configuration page, check the cluster configuration information. If you need to adjust the configuration, click
 to go to the corresponding tab page and configure parameters again.
to go to the corresponding tab page and configure parameters again.Select the checkbox to enable secure communications. For details, see Communication Security Authorization.
Click Create Now.
If Kerberos authentication is enabled, check whether this function is required. If it is, click Continue. If not, click Back to disable it and then proceed with the subsequent step. This option cannot be changed after you create a cluster.
Click Back to Cluster List to view the cluster status.
For details about cluster status during creation, see the description of the status parameters in Table 1.
It takes some time to create a cluster. The initial status of the cluster is Starting. After the cluster has been created successfully, the cluster status becomes Running.
On the MRS management console, a maximum of 10 clusters can be concurrently created, and a maximum of 100 clusters can be managed.
Software Configurations¶
Parameter | Description |
|---|---|
Region | Select a region. Cloud service products in different regions cannot communicate with each other over an intranet. For low network latency and quick access, select the nearest region. |
Cluster Name | The cluster name must be unique. A cluster name can contain 1 to 64 characters. Only letters, digits, hyphens (-), and underscores (_) are allowed. The default name is mrs_xxxx. xxxx is a random collection of letters and digits. |
Cluster Type | The cluster types are as follows:
Note
|
Cluster Version | Currently, MRS 3.1.2-LTS.6, MRS 3.2.0-LTS.2, MRS 3.3.0-LTS.1 and MRS 3.5.0-LTS are supported. The default value displayed on the UI varies depending on the version. |
Components | MRS cluster components. For details about component versions supported by different versions of MRS clusters, see List of MRS Component Versions. |
Component Port | Use the default Open source. |
Hardware Configurations¶
Parameter | Description |
|---|---|
AZ | Select the AZ associated with the region of the cluster. An AZ is a physical area that uses independent power and network resources. AZs are physically isolated but interconnected through the internal network. This improves the availability of applications. You are advised to create clusters in different AZs. |
VPC | A VPC is a secure, isolated, and logical network environment. Select the VPC for which you want to create a cluster and click View VPC to view the name and ID of the VPC. If no VPC is available, create one. |
Subnet | A subnet provides dedicated network resources that are isolated from other networks, improving network security. Select the subnet for which you want to create a cluster. Click View Subnet to view details about the selected subnet. If no subnet is created in the VPC, go to the VPC console and choose Subnets > Create Subnet to create one. For details about how to configure network ACL outbound rules, see How Do I Configure a Network ACL Outbound Rule? Note In MRS, IP addresses are automatically assigned to clusters during cluster creation basically based on the following formula: Quantity of IP addresses = Number of cluster nodes + 2 (one for Manager; one for the DB). In addition, if the Hadoop, Hue, Sqoop, and Presto or Loader and Presto components are selected during cluster deployment, one IP address is added for each component. To create a ClickHouse cluster independently, the number of IP addresses required is calculated as follows: Number of IP addresses = Number of cluster nodes + 1 (for Manager). |
Security Group | A security group is a set of ECS access rules. It provides access policies for ECSs that have the same security protection requirements and are mutually trusted in a VPC. When you create a cluster, you can select Auto create from the drop-down list of Security Group to create a security group or select an existing security group. Note When you select a security group created by yourself, ensure that the inbound rule contains a rule in which Protocol is set to All, Port is set to All, and Source is set to a trusted accessible IP address range. Do not use 0.0.0.0/0 as a source address. Otherwise, security risks may occur. If you do not know the trusted accessible IP address range, select Auto create. |
EIP | After binding an EIP to an MRS cluster, you can use the EIP to access the Manager web UI of the cluster. When creating a cluster, you can select an available EIP from the drop-down list and bind it. If no EIP is available in the drop-down list, click Manage EIP to access the EIPs service page to create one. Note This parameter is valid only in MRS 1.8.0 or later. The EIP must be in the same region as the cluster. |
Parameter | Description |
|---|---|
CPU Architecture | CPU architecture supported by MRS.
|
Common Node Configurations | This parameter is valid only when Cluster Type is set to Custom. For details, see Custom Cluster Template Description. |
Cluster Nodes | MRS provides three types of nodes:
|
Instance Specifications | Instance specifications of Master or Core nodes. MRS supports host specifications determined by CPU, memory, and disk space. Click Note
|
System Disk | Storage type and storage space of the system disk on a node. Storage type can be any of the following:
|
Data Disk | Data disk storage space of a node. To increase data storage capacity, you can add disks at the same time when creating a cluster. The following two application scenarios are involved.
The storage type can be any of the following:
Note More nodes in a cluster require higher disk capacity of Master nodes. To ensure stable cluster running, set the disk capacity of the Master node to over 600 GB if the number of nodes is 300 and increase it to over 1 TB if the number of nodes reaches 500. |
Topology | If the deployment mode in the Common Node does not meet the requirements, set Topology Adjustment to Enable and adjust the instance deployment mode based on service requirements. For details, see Topology Adjustment for a Custom Cluster. This parameter is valid only when Cluster Type is set to Custom. |
Advanced Options¶
Parameter | Description |
|---|---|
Kerberos Authentication | Whether to enable Kerberos authentication when logging in to Manager. This option cannot be changed after you create a cluster.
|
Username | Name of the administrator of Manager. admin is used by default. |
Password | Password of the Manager administrator The following requirements must be met:
Password Strength: The colorbar in red, orange, and green indicates weak, medium, and strong password, respectively. |
Confirm Password | Enter the password of the Manager administrator again. |
Login Mode |
|
Hostname Prefix | Enter the prefix for the computer hostname of an ECS or BMS in the cluster. |
Setting Advanced Options | Advanced function parameters of an MRS cluster. Select Configure. For details, see Table 5. |
Parameter | Description |
|---|---|
Tag | For details, see Adding a Tag to a Cluster/Node. |
Auto Scaling | Auto scaling can be configured only after you specify task node specifications in the Configure Hardware step by referring to Configuring an Auto Scaling Rule. |
Bootstrap Action | For details, see Adding a Bootstrap Action. |
Agency | By binding an agency, ECSs or BMSs can manage some of your resources. Determine whether to configure an agency based on the actual service scenario. For example, you can configure an agency of the ECS type to automatically obtain the AK/SK to access OBS. For details, see Configuring a Storage-Compute Decoupled Cluster (Agency). The MRS_ECS_DEFAULT_AGENCY agency has the OBSOperateAccess permission of OBS and the CESFullAccess (for users who have enabled fine-grained policies), CES Administrator, and KMS Administrator permissions in the region where the cluster is located. |
Metric Sharing | Monitoring metrics of big data components are collected. If a fault occurs when you use a cluster, share the monitoring metrics with technical support for troubleshooting. |
System Disk Encryption | Whether to encrypt data in the system disk mounted to the MRS cluster node. This function is disabled by default. Keys used by encrypted system disks are provided by Key Management Service (KMS) in Data Encryption Workshop (DEW). You do not need to build and maintain the key management infrastructure. To enable this function, you must have the Security Administrator and KMS Administrator permissions. Configure the following parameters to enable this function:
|
Alarm | If the alarm function is enabled, the cluster maintenance personnel can be notified in a timely manner to locate faults when the cluster runs abnormally or the system is faulty. |
Rule Name | Name of the rule for sending alarm messages. The value can contain only digits, letters, hyphens (-), and underscores (_). |
Topic Name | Select an existing topic or click Create Topic to create a topic. To deliver messages published to a topic, you need to add a subscriber to the topic. For details, see Adding Subscriptions to a Topic. A topic serves as a message sending channel, where publishers and subscribers can interact with each other. |
Logging | Whether to collect logs when cluster creation fails. After the logging function is enabled, system logs and component run logs are automatically collected and saved to the OBS file system in scenarios such as cluster creation failures and scale-out or scale-in failures for O&M personnel to quickly locate faults. The log information is retained for a maximum of seven days. |
Failed to Create a Cluster¶
If a cluster fails to be created, the failed task will be managed on the Manage Failed Tasks page. Choose Clusters > Active Clusters. Click  shown in Figure 1 to go to the Manage Failed Tasks page. In the Status column, hover the cursor over
shown in Figure 1 to go to the Manage Failed Tasks page. In the Status column, hover the cursor over  to view the failure cause. You can delete failed tasks by referring to Viewing Failed MRS Tasks.
to view the failure cause. You can delete failed tasks by referring to Viewing Failed MRS Tasks.
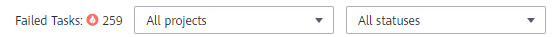
Figure 1 Failed task management¶
Table 6 lists the error codes of MRS cluster creation failures.
Error Code | Description |
|---|---|
MRS.101 | Insufficient quota to meet your request. Contact customer service to increase the quota. |
MRS.102 | The token cannot be null or invalid. Try again later or contact customer service. |
MRS.103 | Invalid request. Try again later or contact customer service. |
MRS.104 | Insufficient resources. Try again later or contact customer service. |
MRS.105 | Insufficient IP addresses in the existing subnet. Try again later or contact customer service. |
MRS.201 | Failed due to an ECS error. Try again later or contact customer service. |
MRS.202 | Failed due to an IAM error. Try again later or contact customer service. |
MRS.203 | Failed due to a VPC error. Try again later or contact customer service. |
MRS.400 | MRS system error. Try again later or contact customer service. |
 to configure the instance specifications, system disk, and data disk parameters of the cluster node.
to configure the instance specifications, system disk, and data disk parameters of the cluster node. : If Kerberos Authentication is disabled, common users can use all functions of an MRS cluster. You are advised to disable Kerberos authentication in single-user scenarios.
: If Kerberos Authentication is disabled, common users can use all functions of an MRS cluster. You are advised to disable Kerberos authentication in single-user scenarios. : If Kerberos Authentication is enabled, common users cannot use the file and job management functions of an MRS cluster and cannot view cluster resource usage or the job records for Hadoop and Spark. To use more cluster functions, the users must contact the Manager administrator to assign more permissions. You are advised to enable Kerberos authentication in multi-user scenarios.
: If Kerberos Authentication is enabled, common users cannot use the file and job management functions of an MRS cluster and cannot view cluster resource usage or the job records for Hadoop and Spark. To use more cluster functions, the users must contact the Manager administrator to assign more permissions. You are advised to enable Kerberos authentication in multi-user scenarios.