Application Process Control Overview¶
HSS can learn the characteristics of application processes on servers and manage their running. Suspicious and trusted processes are allowed to run, and alarms are generated for malicious processes.
Constraints and Limitations¶
Application process control is available only in HSS premium, WTP, and container editions.
To use application process control, ensure the agent installed on the server falls within the following range. For details about how to upgrade the agent, see Upgrading the Agent.
Linux: 3.2.7 or later
Windows: 4.0.19 or later
Process of Using Application Process Control¶
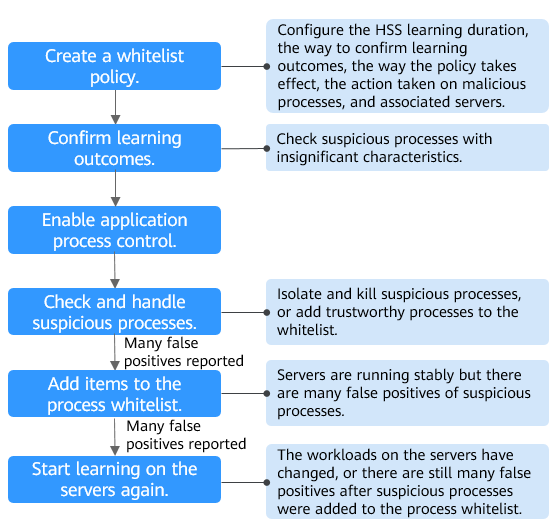
Figure 1 Usage process¶
Operation | Description |
|---|---|
A whitelist policy specifies how HSS learns server behaviors and protect application processes. Application process protection can be enabled only for servers associated with a whitelist policy. | |
After the HSS learns the application processes on servers, there may be some suspicious application processes with insignificant characteristics, and HSS cannot determine whether they are malicious or trustworthy. In this case, you need to confirm the learning outcomes. | |
Enable application process control on the servers associated with a policy. | |
HSS cannot determine whether some suspicious application processes with insignificant characteristics are trustworthy. You need to check their process details, determine whether they are trustworthy, and add them to the process whitelist. | |
(Optional) Add items to the process whitelist. | After HSS completes learning, if it regards many trustworthy application processes as suspicious, you can add these processes to the whitelist. HSS will extend the process whitelist after comparing the fingerprints of the processes it learned and those detected in asset fingerprint scans. |
(Optional) Start learning on the servers again. | If you have added trustworthy processes to the whitelist but there are still many false positives reported, you can let HSS start learning again on the servers. |