Creating a User and Granting EIP Permissions¶
Currently, the EIP service permissions are included in the VPC permissions. For details, see Permissions Management.
This section describes how to use IAM to implement fine-grained permissions control for your VPC resources. With IAM, you can:
Create IAM users for employees based on your enterprise's organizational structure. Each IAM user will have their own security credentials for accessing VPC resources.
Grant users only the permissions required to perform a given task based on their job responsibilities.
Entrust a cloud account or cloud service to perform efficient O&M on your VPC resources.
If your cloud account meets your permissions requirements, you can skip this section.
Figure 1 shows the process flow for granting permissions.
Prerequisites¶
Before granting permissions to user groups, learn about EIP Permissions.
To grant permissions for other services, learn about all permissions supported by IAM.
Process Flow¶
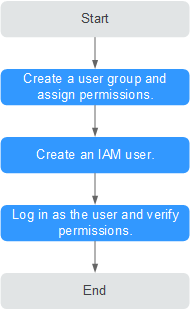
Figure 1 Process for granting VPC permissions¶
On the IAM console, create a user group and grant it permissions (VPC ReadOnlyAccess as an example).
Log in as the IAM user and verify permissions.
In the authorized region, perform the following operations:
Choose Service List > Elastic IP and click Assign EIP in the upper right corner. If a message appears indicating that you have insufficient permissions to perform the operation, the VPC ReadOnlyAccess policy is in effect.
Choose another service from Service List. If a message appears indicating that you have insufficient permissions to access the service, the VPC ReadOnlyAccess policy is in effect.
Example Custom Policies¶
Example 1: Grant permissions to assign and view EIPs
{ "Version": "1.1", "Statement": [ { "Effect": "Allow", "Action": [ " vpc:publicIps:create, vpc:publicIps:list " ] } ] }
Example 2: Grant permission to deny EIP deletion.
A policy with only "Deny" permissions must be used together with other policies. If the permissions granted to an IAM user contain both "Allow" and "Deny", the "Deny" permissions take precedence over the "Allow" permissions.
Assume that you want to grant the permissions of the VPC FullAccess policy to a user but want to prevent them from releasing EIPs. You can create a custom policy for denying EIP release, and attach both policies to the user. As an explicit deny in any policy overrides any allows, the user can perform all operations on EIPs except releasing them. Example policy denying EIP release:
{ "Version": "1.1", "Statement": [ { "Effect": "Deny", "Action": [ "vpc:publicIps:delete" ] } ] }
Example 3: Create a custom policy containing multiple actions.
A custom policy can contain the actions of one or multiple services that are of the same type (global or project-level). Example policy containing multiple actions:
{ "Version": "1.1", "Statement": [ { "Effect": "Allow", "Action": [ "vpc:publicIps:update", "vpc:publicIps:create" ] }, { "Effect": "Deny", "Action": [ "vpc:publicIps:delete" ] } ] }