Creating a Cluster¶
To use cloud GaussDB(DWS), create a data warehouse cluster first.
This section describes how to create a data warehouse cluster on the GaussDB(DWS) management console.
Preparations Before Creating a Cluster¶
You have evaluated the flavor of cluster nodes.
You can select the number of nodes by data volume, service load, and performance. More nodes bring you stronger storage and compute capabilities.
When first using GaussDB(DWS), you can create a cluster with a smaller flavor. Then, you can adjust the cluster scale and node flavor based on the data volume and service load changes without interrupting services. For details, see Scaling Out a Cluster.
Determine the number of nodes that can be used by users.
The number of nodes that can be used by users must meet the following requirements. Otherwise, the system displays a message indicating that the cluster cannot be created.
The number of nodes available to a user depends on the type of product selected. A hybrid data warehouse cluster in standalone mode only has one node, while other cluster types can have three or more nodes. You can view the number of available nodes on the Clusters > Dedicated Clusters page.
Creating a Cluster¶
Log in to the GaussDB(DWS) management console.
In the navigation pane on the left, choose Clusters > Dedicated Clusters.
On the Dedicated Clusters page, click Create GaussDB(DWS) Cluster.
Select Region.
Table 1 Region parameters¶ Parameter
Description
Example Value
Region
Select the actual region where the cluster nodes run.
eu-de
AZ
Select an AZ associated with the cluster region.
For more information, see Regions and AZs.
-Select an AZ. You can select Single AZ or Multi-AZ as required.
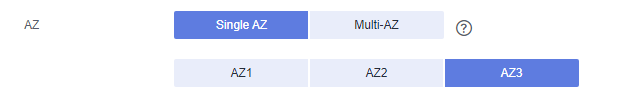
Note
Multi-AZ clusters are supported only by clusters of version 8.2.0.100 or later.
The Multi-AZ option is displayed only if the number of AZs in the selected region is greater than or equal to 3. If this condition is not met, only a single-AZ cluster can be created.
For a multi-AZ cluster, only three AZs can be selected at a time so far. Server nodes are evenly distributed among the three AZs.
The multi-AZ cluster supports only GaussDB(DWS) 2.0 standard data warehouses.
The numbers of nodes in a multi-AZ cluster must be a multiple of 3.
In a multi-AZ cluster, the number of DNs must be less than or equal to 2.
Configure Resource, CPU Architecture, and Node Flavor.
Note
The number of nodes in a new cluster cannot exceed the quota that can be used by a user or 256. If the node quota is insufficient, click Increase quota to submit a service ticket and apply for higher node quota.
Table 2 Node configuration parameters¶ Parameter
Description
Example Value
Resource
Product type. It can be:
Standard data warehouse: It can analyze hot and cold data and is highly cost-effective. Its storage and computing resources are not limited, and can be elastically scaled and billed per use. It is suitable for the converged analysis that requires integrated databases, warehouses, marts, and lakes. It is most suitable for OLAP workloads.
Standard
Compute Resource
It can be:
ESC: Scalable, reliable, and high-throughput virtual block storage is provided in a distributed architecture. This ensures that data can be quickly migrated and restored if any data replica is unavailable, preventing data from being lost because of a single hardware fault. Backup and restoration can be performed on ECSs and EVS disks. You can configure automatic backup policies for them.
-Storage Type
It can be:
Cloud SSD
-CPU Architecture
The CPU architecture includes:
x86
-Node Flavor
Select the desired node flavor based on service requirements. Each node flavor displays the vCPU, memory, and recommended application scenario.
dws.m3.xlarge
Hot storage
Available storage capacity of each node.
Note
The storage capacity you apply for has the necessary file system overhead, which includes index nodes and the space required for database running. The storage space must be an integer multiple of 100.
200 GB per node is the actual storage capacity for service data. For example, if the number of nodes is set to 3, the total resource capacity is 600 GB.
By default, tablespaces are automatically created when you configure cold and hot data storage. You do not need to manually create tablespaces. This feature is supported only in clusters of 8.1.3 and later versions.
-Cold storage
You are advised to store cold data in OBS.
-Nodes
Specify the number of nodes in the cluster.
The number of nodes ranges from 3 to 256.
3
Total
Displays the total capacity of a cluster.
The storage capacity of each flavor is the actual database space used for storing data. The displayed storage capacity has deducted the disk space consumed by backups and RAIDs.
-Click Next: Configure Network.
Configure the network.
Table 3 Network parameters¶ Parameter
Description
Example Value
VPC
Specify a virtual private network for nodes in a cluster to isolate networks of different services.
If you create a data warehouse cluster for the first time and have not configured the VPC, click View VPC. On the VPC management console that is displayed, create a VPC that satisfies your needs.
For details about how to create a VPC, see "VPC and Subnet > Creating a VPC" in the Virtual Private Cloud User Guide.
After selecting a VPC from the drop-down list, click View VPC to enter the VPC management console and view the detailed information about the VPC.
You can click
 to refresh the options in the VPC drop-down list.
to refresh the options in the VPC drop-down list.vpc-dws
Subnet
Specify a VPC subnet.
A subnet provides dedicated network resources that are isolated from other networks, improving network security.
Note
After a cluster is created, the subnet cannot be modified. If you need to modify the subnet, you can restore the snapshot of the cluster to a new cluster. The data of the new cluster is the same as that of the old cluster, and the subnet can be modified when the new cluster is created.
subnet-dws
Security Group
Specify a VPC security group.
A security group restricts access rules to enhance security when GaussDB(DWS) and other services access each other.
Automatic creation
If Automatic creation is selected, the system automatically creates a default security group. This option is selected by default.
The rule of the default security group is as follows: The outbound allows all access requests, while the inbound is open only to the database port that you set to connect to the GaussDB(DWS) cluster.
The format of the default security group name is dws-<Cluster_name>-<Cluster_database_port>, for example, dws-dws-demo-8000.
Note
If the quotas of the security group and the security group rule are insufficient, an error message will be displayed after you submit the cluster creation application. Select an existing group and retry.
Manual creation
You can also log in to the VPC management console to manually create a security group. Then, go back to the page for creating data warehouse clusters, click
 next to the Security Group drop-down list to refresh the page, and select the new security group.
next to the Security Group drop-down list to refresh the page, and select the new security group.To enable the GaussDB(DWS) client to connect to the cluster, you need to add an inbound rule to the new security group to grant the access permission to the database port of the GaussDB(DWS) cluster. The following is an example of an inbound rule..
Protocol: TCP
Port: 8000. Use the database port set when creating the GaussDB(DWS) cluster. This port is used for receiving client connections to GaussDB(DWS).
Source: Select IP address and use the host IP address of the client host, for example, 192.168.0.10/32.
The security group of a cluster cannot be changed but can be modified. For details, see Modifying a Security Group.
Automatic creation
Public Network Access
Specify whether users can use a client to connect to a cluster's database over the Internet. The following methods are supported:
Do not use: The EIP is not required.
Automatically assign: Users specify the bandwidth of the EIP and the system automatically assigns an EIP that exclusively uses bandwidth to each cluster so that users can use the EIP to access the cluster over the Internet. The bandwidth name of an automatically assigned EIP starts with the cluster name.
Specify: A specified EIP is bound to the cluster. If no available EIPs are displayed in the drop-down list, click Create EIP to go to the Elastic IP page and create an EIP that satisfies your needs. You can set the bandwidth as needed.
Note
If you use the EIP binding function for the first time in each project of each region, the system prompts you to create the DWSAccessVPC agency to authorize GaussDB(DWS) to access VPC. After the authorization is successful, GaussDB(DWS) can switch to a healthy VM when the VM bound with the EIP becomes faulty.
By default, only cloud accounts or users with Security Administrator permissions can query and create agencies. By default, the IAM users in those accounts cannot query or create agencies. When the users use the EIP, the system makes the binding function unavailable. Contact a user with the DWS Administrator permissions to authorize the agency on the current page.
Do not use indicates disabling access to the cluster over the public network. After a cluster is created, if you want to access it over the public network, bind an EIP to the cluster and create a public network domain name. For details, see Creating a Public Network Domain Name.
Automatically assign
ELB
Specifies whether ELB is bound. With ELB health checks, CN requests of a cluster can be quickly forwarded to normal CNs. If a CN is faulty, the workload can be immediately shifted to a healthy node, minimizing cluster access faults.
Do not use: The load balancer is not used.
Specify: Specify an ELB to be bound to the cluster. If no available load balancers are displayed in the drop-down list, click Create ELB to go to the Elastic Load Balance page and create a load balancer as needed.
Specify
Bandwidth
When EIP is set to Automatically assign, you need to specify the bandwidth of the EIP, which ranges from 1 Mbit/s to 100 Mbit/s.
50Mbit/s
Click Next: Configure Advanced Settings.
Configure cluster parameters.
Table 4 Cluster parameters¶ Parameter
Description
Example Value
Cluster Name
Set the name of the data warehouse cluster.
The cluster name contains 4 to 64 case-insensitive characters and must start with a letter. Only letters, digits, hyphens (-), and underscores (_) are allowed.
Note
Only in 8.3.1 and later versions, you can change the cluster name after a cluster is created.
dws-demo
Cluster Version
Displays the version of the database instance installed in the cluster. The figure is for reference only.
-
Default Database
The default database name of the cluster is gaussdb.
Note
This name cannot be changed.
gaussdb
Administrator Account
Set the database administrator name.
The administrator username must:
Consist of lowercase letters, digits, or underscores.
Start with a lowercase letter or an underscore.
Contain 6 to 64 characters.
Cannot be a keyword of the GaussDB(DWS) database. For details about the keywords of the GaussDB(DWS) database, see "SQL Reference > Keyword" in the Data Warehouse Service (DWS) Developer Guide.
dbadmin
Administrator Password
Set the password of the database administrator account.
The password complexity requirements are as follows:
Consists of 12 to 32 characters.
Cannot be the username or the username spelled backwards.
Must contain at least three of the following character types: uppercase letters, lowercase letters, digits, and special characters
~!?,.:;-_'"(){}[]/<>@#%^&*+|\=`Passes the weak password check.
Note
Change the password regularly and keep it secure.
-Confirm Password
Enter the database administrator password again.
-Database Port
Specify the port used when the client or application connects to the database in the cluster.
The port number ranges from 8000 to 30000.
Note
The database port of a created cluster cannot be changed. You can specify the database port only when creating a cluster.
8000
Configure the enterprise project to which the cluster belongs. You can configure this parameter only when the Enterprise Project Management service is enabled. The default value is default.
An enterprise project facilitates project-level management and grouping of cloud resources and users.
You can select the default enterprise project default or other existing enterprise projects.
Configure advanced settings. Select Default to keep the default values of the advanced parameters. You can also select Custom to modify the values.
CNs
CNs receive access requests from the clients and return the execution results. In addition, a CN splits and distributes tasks to the DNs for parallel execution.
The value ranges from 3 to the number of cluster nodes. The maximum value is 20 and the default value is 3. In a large-scale cluster, you are advised to deploy multiple CNs.
Tag
A tag is a key-value pair used to identify a cluster. For details about the keys and values, see Table 5. By default, no tag is added to the cluster.
For more information about tags, see Overview.
Table 5 Tag parameters¶ Parameter
Description
Example Value
Key
You can select:
Select a predefined tag key or an existing resource tag key from the drop-down list of the text box.
Note
To add a predefined tag, you need to create one on TMS and select it from the drop-down list of Tag key. You can click View predefined tags to enter the Predefined Tags page of TMS. Then, click Create Tag to create a predefined tag. For more information, see Management > Predefined Tags > Creating Predefined Tags in the Tag Management Service User Guide.
Enter a tag key in the text box. A tag key can contain a maximum of 36 characters. It cannot be an empty string or start or end with a space.
The value cannot contain the following characters:
=*<>\,|/Note
A key must be unique in a given cluster.
key01
Value
You can select:
Select a predefined tag value or resource tag value from the drop-down list of the text box.
Enter a tag value in the text box. A tag value can contain a maximum of 43 characters, which can be an empty string. It cannot start or end with a space.
The value cannot contain the following characters:
=*<>\,|/
value01
Click Next: Confirm.
Note
If the number of requested nodes, vCPU (cores), or memory (GB) exceed the user's remaining quota, a warning dialog box is displayed, indicating that the quota is insufficient and displaying the detailed remaining quota and the current quota application. You can click Increase quota in the warning dialog box to submit a service ticket and apply for higher node quota.
Click Create Now.
After the submission is successful, the creation starts. Click Back to Cluster List to go back to the Dedicated Clusters page. The initial status of the cluster is Creating. Cluster creation takes some time. Clusters in the Available state are ready for use.